Description
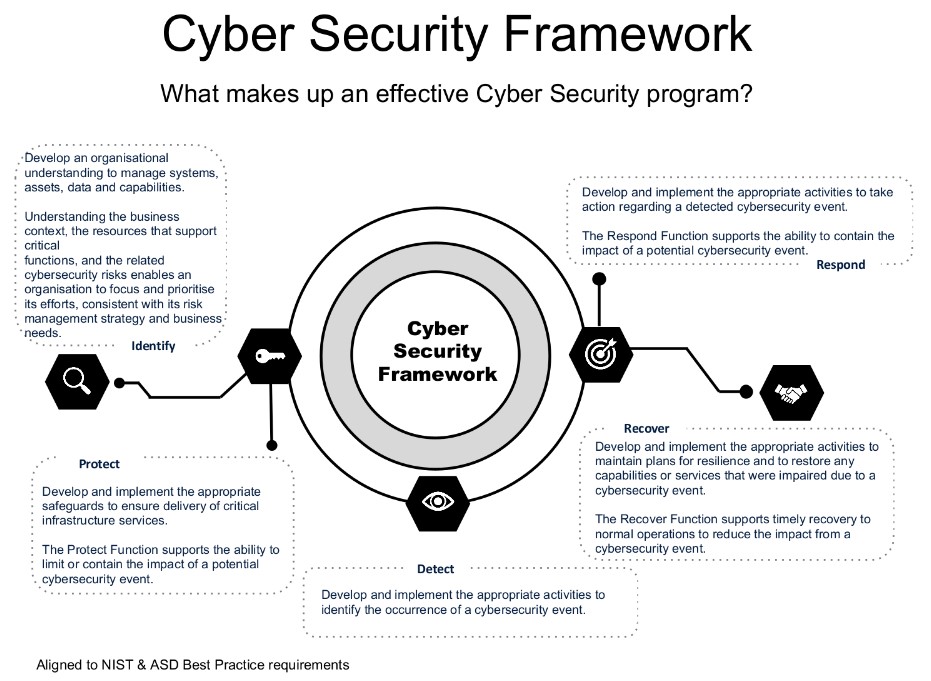
Cyber security risks are increasing, driven by global connectivity and the use of cloud services to store sensitive data. Data breaches and cyber attacks are also on the rise causing irreversible reputational damage. Gone are the days of simple firewall and antivirus software as the sole security measures. Included in this suite you will find guidance on:
- Cyber Governance mandates
- Cyber resilience measures
- Roles and responsibilities
- Responding to incidents
- Tools for staff training